Large-scale Roblox hacking operation shut down by Ukrainian authorities

Ukrainian police arrested three hackers who hijacked 610,000 Roblox accounts and sold them for $225,000 in profit.
Police in Ukraine arrested three suspects accused of hacking over 610,000 Roblox accounts and selling them for about $225,000. Officers carried out multiple searches in Lviv, seizing cash, phones, computers, laptops, tablets, and USB drives. The operation disrupted a large-scale account theft scheme targeting gamers and online platforms.
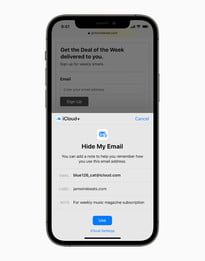
A 19-year-old from Drohobych, with two accomplices, used stolen session cookies to access accounts without passwords. They scanned over 610,000 profiles, identifying those with valuable virtual currency or rare items. Using specialized tools, they verified access and compiled 357 files of high-value accounts. The group then sold these on Russian platforms, receiving payments in cryptocurrency.
“From October 2025 to January 2026, over 610,000 user accounts were checked in this manner. They selected those that contained the most valuable digital resources. During investigative actions, law enforcement discovered 357 files with such accounts.” reads the press release published by Prosecutor General’s Office. “Subsequently, these files were sold on Russian resources, with payment made to a cryptocurrency wallet. According to preliminary information, the profit from the sale of accounts during the entire period of the group’s activities could reach nearly 10 million UAH.”
Ukrainian Police carried out 10 searches, seizing computers, phones, storage devices, bank cards, notes, and cash over €2,500 and $35,000. Suspects were charged with theft in conspiracy and unauthorized interference in information systems causing data leaks. A 44-year-old associate was also detained for drug possession with intent to sell after cannabis-like substances were found.

“Under the procedural guidance of the Lviv Regional Prosecutor’s Office and the Frankivsk District Prosecutor’s Office of Lviv, the group members were informed of suspicions of theft by prior conspiracy of a group of individuals, as well as unauthorized interference in the operation of information (automated) systems, which led to the leakage of information by prior conspiracy of a group of individuals (Part 4 of Article 185, Part 5 of Article 361 of the Criminal Code of Ukraine).” concludes the press release.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Roblox)