From Android TVs to routers: the xlabs_v1 Mirai-based botnet built for DDoS attacks

A new Mirai‑based botnet, xlabs_v1, hijacks ADB‑exposed IoT devices for powerful DDoS attacks, with 21 flooding methods and DDoS‑for‑hire use.
A new Mirai‑derived botnet called xlabs_v1 is hijacking internet‑exposed devices running Android Debug Bridge (ADB) and using them for large‑scale DDoS attacks. Hunt.io discovered the bot on an unsecured server, it includes 21 flood techniques across TCP, UDP, and raw protocols, allowing it to bypass basic protections. It appears to be sold as a DDoS‑for‑hire service, especially for targeting game and Minecraft servers.
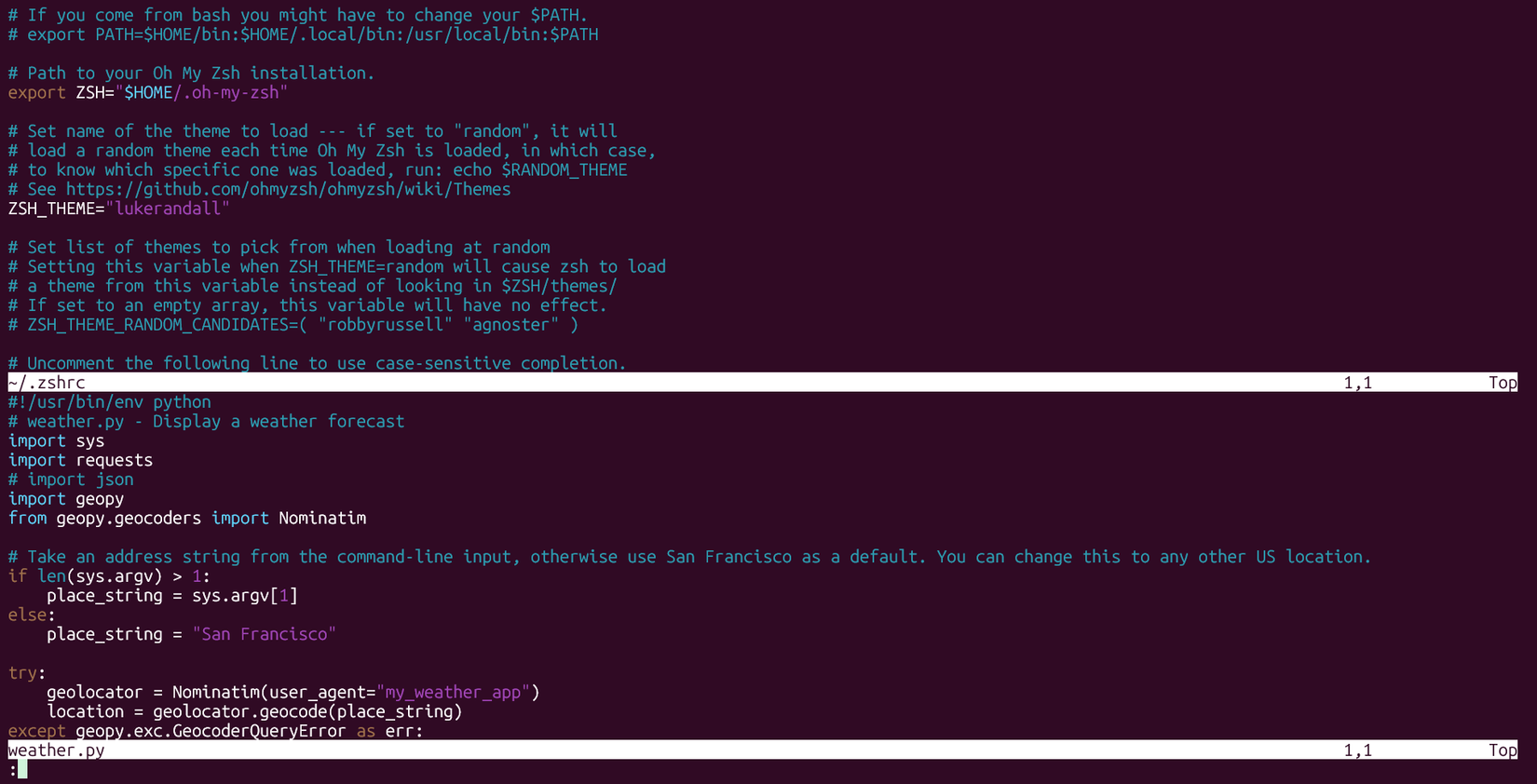
During routine monitoring, researchers spotted an exposed directory on a Netherlands‑hosted server (176.65[.]139.44) used for bulletproof hosting. The operator had left their entire toolkit publicly accessible over TCP/80 with no authentication, allowing investigators to index everything before the attacker realized it was exposed.

Open access to the server revealed a six‑file toolkit instead of a login page, exposing binaries and text files with no authentication. Two files were auto‑tagged as malicious: arm7 (Mirai) and payloads.txt (exploit content), suggesting the operator was using analyst‑grade tools on an unsecured host. The directory held about 200 KB of data, including the packed ARM bot, an unstripped x86‑64 debug build, ADB infection one‑liners, a SOCKS5 proxy, and a placeholder targets file. The debug build’s intact symbols made reconstructing the bot’s behavior straightforward.
“The xlabs_v1 codebase reads as a focused commercial product rather than an opportunistic Mirai derivative. Its twenty-one flood variants, ChaCha20 string protection, OpenNIC-aware DNS resolution, and Speedtest-driven bandwidth profiling are subsystems aimed at a single outcome: keeping a fleet of compromised IoT devices reachable, accountable, and profitable for the operator. Everything else in the binary serves that goal or protects it.” reads the report published by Hunt.io.
xlabs_v1 botnet is built entirely for commercial DDoS‑for‑hire operations, with no added features like credential theft that could increase detection risk. Its core function is to receive attack commands and launch one of 21 flood variants, many aimed at game servers, including RakNet floods for Minecraft and OpenVPN‑shaped UDP traffic to evade filters. Delivered through ADB exploits, the ARMv7 bot targets Android TVs, set‑top boxes, and IoT hardware, part of a global surface of more than 4 million devices with TCP/5555 exposed.
“nfection vector is Android Debug Bridge on TCP/5555, with multi-architecture builds covering ARM, MIPS, x86-64, ARC, and Android APK, meaning any internet-exposed device running ADB is a potential target: Android TV boxes, set-top boxes, smart TVs, residential routers, and any IoT-grade hardware shipping with ADB enabled by default.” continutes the report.
Once installed, the bot hides infection tags, profiles each device’s bandwidth by opening 8,192 TCP sockets, and reports Mbps to its panel so the operator can assign price tiers. It also kills competing botnets by scanning /proc, terminating rival processes, and removing malware on port 24936.
For resilience, xlabs_v1 resolves its C2 via OpenNIC, falls back to a firewall‑punching SOCKS‑style listener on TCP/26721, and masks itself as /bin/bash to evade casual inspection. Sensitive strings, including the C2 domain xlabslover.lol, the operator handle Tadashi, and the agent tag xlabs_v1, are encrypted with ChaCha20 but easily recovered due to key reuse.
Its command‑and‑control uses a custom TCP protocol, supporting bandwidth probes, updates, self‑restart, and attack dispatch. Together, these techniques reveal a sophisticated, commercially motivated DDoS botnet engineered for persistence, evasion, and profit.
Analysis of the xlabs_v1 botnet’s infrastructure begins with its C2 domain, xlabslover[.]lol, which resolves to a single IP in the Netherlands hosted by Offshore LC. The domain uses Ultahost nameservers, a provider often linked to bulletproof hosting, and shows no prior malware detections, suggesting a recently deployed C2.
Pivoting from the domain to its IP (176.65.139[.]134) reveals SSH as the only open port, plus past honeypot activity involving HTTP and .env‑file scanning. SSL history shows unusual self‑signed certificates, including one with the CN “Godisgood”, previously used on another IP in Germany, indicating the same operator managing multiple servers.
Three hosts within the 176.65.139.0/24 netblock appear tied to the botnet: .44 (staging), .42 (distribution), and .9 (additional distribution). Hunt.io captured open directories on these systems containing Mirai‑tagged binaries, multi‑architecture payloads, and ADB exploitation scripts.
Historical scans confirmed Mirai C2 activity in late March and early April 2026, consistent with the botnet’s active deployment period and revealing a consolidated, bulletproof infrastructure supporting xlabs_v1.
The operator behind the botnet uses the handle Tadashi, embedded in each build, while the botnet brand xlabs_v1 appears in every C2 registration, hinting at future versions. A development tag, aterna, shows earlier branding before release. OSINT searches linking “Tadashi,” “xlabs,” and “xlabslover” may reveal the operator’s DDoS‑for‑hire storefront. A decrypted banner also exposes hostility toward a rival fork, xlab 2, suggesting a code split or underground feud. Nearby infrastructure in the same netblock has hosted cryptojacking tools, though overlap with the xlabs operation remains unconfirmed.
“In commercial-criminal terms, xlabs_v1 is mid-tier. It is more sophisticated than the typical script-kiddie Mirai fork (which would lack the ChaCha20 layer, the multi-architecture binary set, the bandwidth profiling, and the registered-attack diversity), but less sophisticated than the top tier of commercial DDoS-for-hire operations (which would use TLS on the C2 channel, would not ship a debug build to production paths, would rotate cryptographic material across builds, and would not ship a hard-coded competitor-rivalry banner).” concludes the report. “This operator is competing on price and attack variety, not technical sophistication. Consumer IoT devices, residential routers, and small game-server operators are the target. Treat it accordingly.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, xlabs_v1 botnet)