TL;DR
ShinyHunters breached Instructure’s Canvas learning management system, claiming 3.65 terabytes of data from 275 million users across 9,000 institutions worldwide, including private messages between students and teachers. Forty-four Dutch universities and schools are confirmed affected, and the breach, the second at Instructure in eight months, exposes the structural risk of vendor concentration in education technology.
The largest education data breach in history was not an attack on a school. It was an attack on a vendor. On 30 April, hackers exploited a vulnerability in the systems of Instructure, the company that makes Canvas, the learning management system used by 41 per cent of higher education institutions across North America.
The criminal group ShinyHunters, which previously orchestrated the Snowflake supply chain attacks that compromised Ticketmaster and AT&T, claims to have stolen 3.65 terabytes of data affecting 275 million users across nearly 9,000 educational institutions worldwide, including private messages between students, teachers, and staff.
In the Netherlands, 44 universities and schools are confirmed affected, from the University of Amsterdam and Vrije Universiteit to The Hague University of Applied Sciences. Dutch authorities have told students and staff to be vigilant. The hackers have told Instructure to pay up by 8 May or the data goes public.
And the breach exposes a structural vulnerability in the way education has been digitised: the schools did not choose to be attacked, and they could not have prevented it, because the decision to entrust student data to a single vendor was made years ago, and the vendor’s security was never theirs to control.
The company
Instructure was founded in 2008 and built Canvas into the dominant learning management platform in the United States, overtaking Blackboard to claim 31 per cent of the North American higher education LMS market by 2018. The company went public in 2015, was taken private by Thoma Bravo in a two billion dollar deal in 2020, and was sold again to KKR and Dragoneer Investment Group in November 2024 for 4.8 billion dollars.
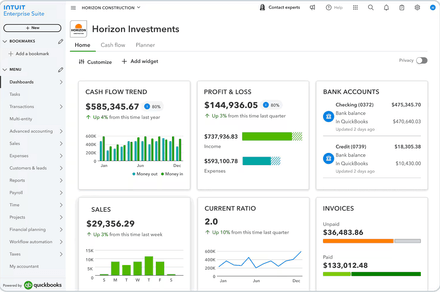
The company now operates as a private entity owned by one of the world’s largest alternative asset managers, serving approximately 200 million learners across more than 100 countries. Its products include Canvas LMS, Canvas Studio for video-based learning, and Mastery Assessment for competency tracking. The platform is embedded in the daily academic life of students from secondary school to postgraduate programmes, handling course materials, assignment submissions, grades, and, critically, direct messages between students and educators.
This is Instructure’s second confirmed breach in approximately eight months. In September 2025, ShinyHunters exploited a social engineering attack against the company’s Salesforce environment. The April 2026 attack exploited a vulnerability in Instructure’s production systems, which the company says has since been patched. Instructure’s chief information security officer Steve Proud notified customers on 1 May that the company had experienced a cybersecurity incident, confirming that the exposed data may include names, email addresses, student identification numbers, and Canvas Inbox and Discussion messages.
The company says there is no indication that dates of birth, government identifiers, financial information, or passwords were compromised. But the inclusion of private messages, which could contain phone numbers, home addresses, and personal information shared in the expectation of privacy, makes the breach qualitatively different from a typical email-and-name data leak.
The attackers
ShinyHunters is a criminal hacking and extortion group that has been active since 2020 and has become one of the most prolific data thieves in the world. The group, believed to comprise a small number of core members based in Canada and France, specialises in targeting companies that provide services to multiple organisations, allowing a single breach to cascade across thousands of victims.
In 2024, ShinyHunters orchestrated the Snowflake supply chain campaign, compromising approximately 165 organisations including Ticketmaster, where 560 million records were exposed, and AT&T, where data on 110 million customers was stolen. AT&T paid a 370,000 dollar ransom to have the data deleted. In March 2026, ShinyHunters breached the European Commission, leaking 350 gigabytes of data from 42 internal clients and at least 29 EU entities. The group’s method is consistent: identify a vendor or platform with access to large volumes of data, exploit a vulnerability or social engineering vector, exfiltrate the data, and demand payment under threat of public release.
The Instructure breach follows this pattern precisely. ShinyHunters posted its claim on a dark web forum on 2 May, listing 8,809 school districts, universities, and online education platforms with per-institution record counts. The group warned Instructure to “make the right decision” before 6 May, later extended to 8 May, or face the release of the full dataset along with what it described as “several annoying digital problems.” The hackers claim to possess billions of private messages.
The cybersecurity industry has been predicting that 2026 would be the year of governed security AI, with automated threat detection and response systems reaching operational maturity. Instructure’s breach suggests the governance gap between enterprise security posture and attacker capability remains wide, and that the organisations most vulnerable are not the ones with the weakest security but the ones whose vendors have the widest blast radius.
The vulnerability
The structural problem the breach exposes is vendor concentration. Canvas dominates its market because it is good: the platform is well-designed, reliable, and deeply integrated into institutional workflows. But dominance means that a single security failure at a single company can compromise the academic records and private communications of students across 9,000 institutions in dozens of countries simultaneously. The schools and universities affected by the breach had no role in the security decisions that allowed it. They were not consulted about the vulnerability that was exploited.
They cannot independently audit the security of the systems that hold their students’ data. They are, in the language of cybersecurity, downstream. Europe has been dismantling and rewriting its own regulatory rulebook in an attempt to balance innovation and security, but the Canvas breach demonstrates that the education sector sits in a regulatory gap: schools are subject to data protection obligations under GDPR and, in the Netherlands, the new Cybersecurity Act transposing NIS2, yet their ability to meet those obligations depends on the security practices of a private company owned by a private equity firm on another continent.
The EU’s ongoing struggles to finalise its AI Act amendments illustrate the broader challenge: regulation consistently lags behind the speed at which technology concentrates data and the speed at which attackers exploit that concentration. NIS2 imposes breach reporting requirements and fines of up to 10 million euros or two per cent of global turnover for non-compliance, and the Cyber Resilience Act, which begins to apply in September 2026, will mandate vulnerability reporting for products with digital elements.
But the education sector’s reliance on a small number of dominant platforms means that compliance at the institutional level cannot prevent a breach at the vendor level. The 44 Dutch institutions affected by the Canvas breach may have been fully compliant with every applicable regulation and still had no capacity to prevent or mitigate the attack.
The pattern
The Instructure breach is the latest in a series of attacks on education technology vendors that collectively demonstrate the sector’s status as one of the softest targets in the global economy. In December 2024, PowerSchool, which provides administrative software to K-12 schools, was breached, and the attacker demanded 2.85 million dollars in ransom, which the company paid.
Education technology platforms have become some of the most widely used consumer applications in the world, with companies like Duolingo reporting 56.5 million daily active users, yet the industry’s security maturity has not kept pace with its user growth. The edtech sector collects sensitive data on minors, stores private academic communications, and operates with a user base that has limited capacity to protect itself. The combination of high data value, low security investment relative to other sectors, and a user base that includes children makes education technology an attractive target for criminal groups.
The question of whether European digital regulation can deliver both innovation and security is not abstract for the 44 Dutch institutions now advising students to change passwords and monitor their accounts. The private equity ownership model that has shaped Instructure’s trajectory, from Thoma Bravo’s two billion dollar take-private to KKR’s 4.8 billion dollar acquisition, optimises for revenue growth, cost efficiency, and eventual exit. Whether it optimises for security investment is a question that the breach has answered. Instructure’s Canvas is a product that 200 million learners depend on daily.
The company that owns it was breached twice in eight months by the same criminal group. The schools had no say in the vendor’s security architecture, no visibility into its vulnerability management, and no ability to prevent the compromise of their students’ data. The students have been told to be vigilant. Vigilance, in this context, means accepting that the data is gone and hoping it is not weaponised. The vendor model that digitised education at scale also concentrated the risk at scale, and the breach is the cost.