Cyber incidents in 2026 are faster, stealthier and increasingly more automated. From AI-driven phishing to SaaS account takeovers and supply chain compromises, cyber crime is more evolved and more complicated than it’s ever been before. The question we are asking now is this – Are your incident response playbooks ready for the threat landscape of 2026?
A well-designed playbook transforms chaos into coordinated action. It should help your teams detect, contain, and recover from cyber incidents with speed and precision. In 2026, it’s important that your playbook reflects the reality of the AI dominated era. The Incident Response Playbook Scenarios that you use should reflect modern day threats. In this article, we cover some of the most important triggers and Incident Response Playbook Examples that you should prioritise in 2026.
What is a Cybersecurity Incident Response Playbook?
A Cyber Incident Response Playbook is a scenario-specific, step-by-step guide that defines exactly how your organisation should respond to a specific cyber incident. Unlike a Cyber Incident Response Plan, which is a larger roadmap, a playbook is specific to incident types.
A good playbook includes:
- Trigger conditions
- Roles and responsibilities
- Technical and business actions
- Communication workflows
- Escalation paths
In simple terms, a Cyber Incident Response Plan lays out the overall organisational strategy in case of a cybersecurity event. A Playbook, on the other hand, defines specific steps that need to be executed in case of a specific type of attack.
Why Playbooks Are Critical in 2026
Cyber threats have evolved significantly in 2026. From AI-powered phishing that bypasses traditional detection to SaaS and cloud breaches which dominate attack vectors, attacks today look very different from just 12 months ago. Ransomware now includes data exfiltration and extortion. In many cases, the goal of cyber threat actors is pure disruption.
In this new world order, playbooks ensure faster containment. They reduce business disruption with consistent and auditable responses. They also create clear accountability structures under pressure. More importantly, current regulations the world over, including EU DORA and NIS2, expect tested response readiness.
What are Cyber Incident Response Playbook Scenarios?
In 2026, no two attacks are exactly alike. In fact, malicious threat actors are consistently ahead of the curve, innovating and coming up with new tactics and attack vectors almost every day. This is why a “one-size-fits-all” response will not work anymore. Instead, you need to build tailored Incident Response playbooks for specific situations such as a ransomware outbreak, a data theft incident or an insider threat.
Each scenario-based playbook outlines clear steps for detection, containment, eradication, and recovery for each of these cybersecurity events. The playbooks should also define the communication flow, escalation paths, and responsibilities of different stakeholders.
For example, a ransomware scenario will prioritise isolating infected systems and preserving backups. A data theft playbook, on the other hand, will focus on forensic analysis, regulatory reporting, and customer communication. Insider threat scenarios require sensitive handling of HR and legal processes alongside technical investigation. The playbook for this scenario will reflect this sensitivity in crisis management and communication.
By having dedicated playbooks for different scenarios, your organisation can act with speed and precision when the unexpected happens. These scenario-driven responses reduce confusion and minimise business disruption. Most importantly, they instil confidence across the workforce that the organisation is prepared for whatever form a cyber attack may take.
If you do not have different playbooks for different attack scenarios, you might want to start building them today after going through the next section. And if you do have ready playbooks, consider our Incident Response Playbooks Creation and Review services. Having your playbooks reviewed by top cybersecurity experts and incorporating their recommendations can give you unbridled peace of mind.
Top Cybersecurity Incident Response Playbook Scenarios for 2026
Now that we have established why scenario-specific playbooks are essential, let us examine the core cyber incident response playbook examples your organisation should prioritise developing for 2026:
1. Ransomware + Data Exfiltration Playbook
Why it matters: Still the #1 high-impact attack
Key actions:
- Isolate infected systems immediately
- Disable lateral movement pathways
- Preserve forensic evidence
- Assess data exfiltration risk
- Coordinate legal + regulatory response
Modern ransomware is no longer just encryption. It’s double extortion and your team must be prepared for this modern reality.
2. Business Email Compromise (BEC) Playbook
Why it matters: Leading cause of financial fraud
Key actions:
- Identify compromised accounts
- Reset credentials and revoke sessions
- Analyse email logs for spread
- Notify affected stakeholders
- Reverse fraudulent transactions (if possible)
3. SaaS / Cloud Account Compromise Playbook
Why it matters: It is a high priority scenario in 2026
Key actions:
- Revoke OAuth tokens and API access
- Audit integrations and permissions
- Analyse access logs for anomalies
- Secure identity provider (IdP)
- Enforce MFA resets across users
4. Supply Chain / Third-Party Breach Playbook
Why it matters: Increasingly common attack vector
Key actions:
- Identify affected vendors
- Isolate third-party integrations
- Assess downstream exposure
- Activate vendor risk escalation
- Communicate with regulators if required
5. Insider Threat Playbook
Why it matters: Complex and sensitive
Key actions:
- Monitor suspicious behaviour
- Preserve evidence discreetly
- Coordinate with HR + legal
- Restrict access without alerting subject
- Conduct internal investigation
6. Data Breach & Regulatory Response Playbook
Critical for GDPR, NIS2, DORA
Key actions:
- Confirm breach scope
- Classify affected data
- Notify regulators within deadlines
- Prepare customer communication
- Maintain audit-ready documentation
7. DDoS / Service Disruption Playbook
Why it matters: Business continuity risk
Key actions:
- Activate traffic filtering / CDN
- Engage ISP / mitigation providers
- Monitor service availability
- Communicate with customers
- Track attacker patterns
How to Build a High-Quality Playbook in 2026?
A Cyber Incident Response Playbook is no longer a luxury. In 2026, it’s a necessity for businesses who wish to weather the cyber threat storm. An effective playbook is not just a document. It is a blueprint for operational success.
At Cyber Management Alliance, we specialise in developing and optimising incident response playbooks that actually work in the real world. We’ve helped thousands of businesses build actionable, compliant and tested IR plans and playbooks that actually work.
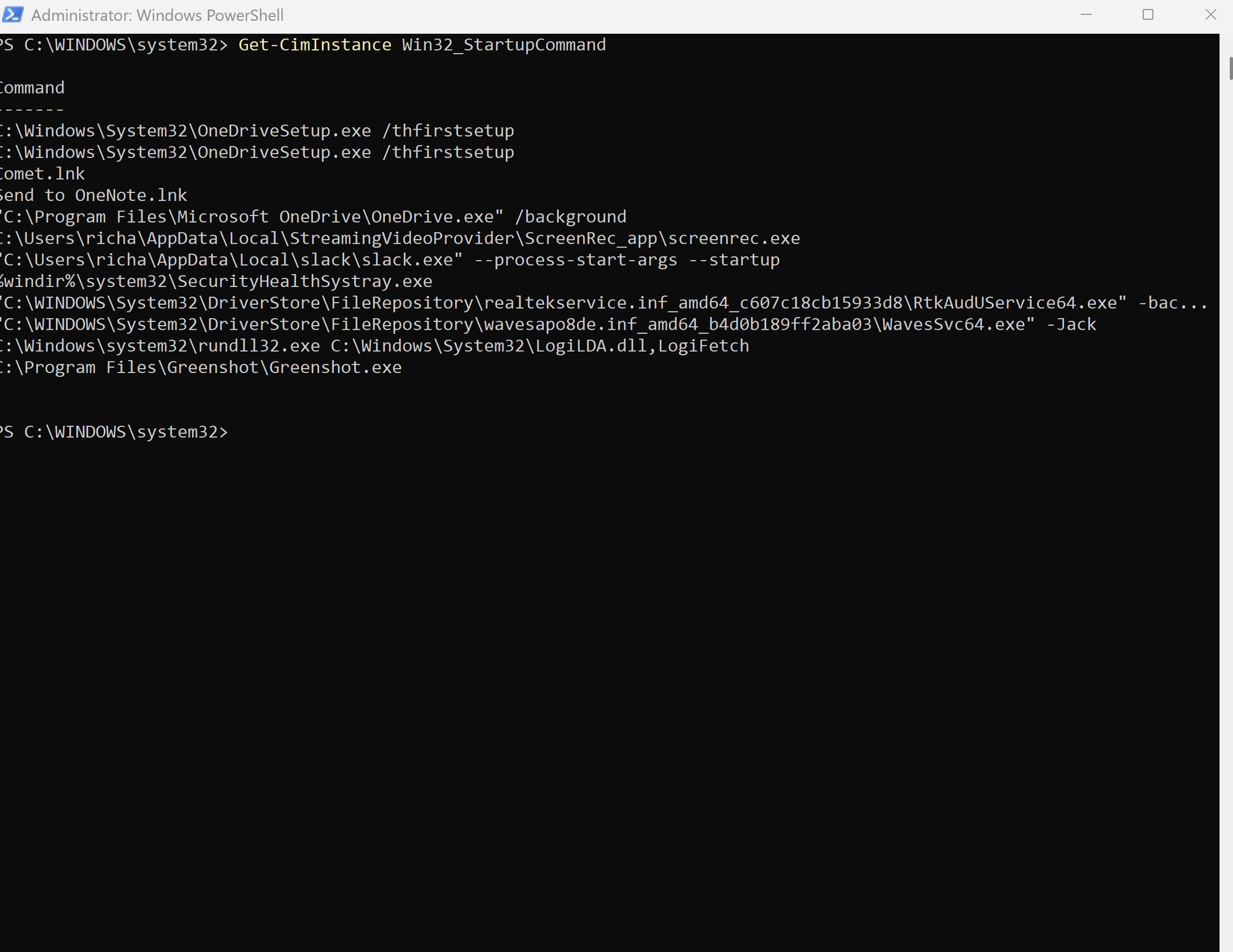
Here’s a quick checklist by our experts of what an IR Playbook must contain in 2026
- Clear triggers for activation
- Role-based responsibilities
- Decision points (when to escalate)
- Tool-specific actions (SIEM, EDR, cloud logs)
- Communication workflows
- Post-incident review steps
Using the examples shared above, you can now start building new playbooks from scratch and improve upon existing incident response processes. You must also make sure that the playbooks are tested regularly through cyber drills. Simulate cyber attack scenarios and see if the playbooks created for those specific situations hold water under pressure.
Playbooks must also be regularly updated based on the learnings/feedback from your cyber tabletop exercises, apart from real-world threat intelligence.
FAQs on Incident Response Playbooks in 2026
1. What is an example of an incident response playbook?
A ransomware playbook is a common example. It includes steps to detect the attack, isolate systems, contain spread, recover data, and manage communication.
2. How many playbooks should an organisation have?
At minimum, you must have a playbook for each of the below triggers/events:
- Ransomware
- Data breach
- Phishing/BEC
- Insider threat
- Cloud/SaaS compromise
3. What is the difference between an IR plan and a playbook?
An Incident Response plan defines strategy and governance. A playbook provides step-by-step execution for specific scenarios.
4. Are playbooks required for compliance?
Yes. Frameworks like the GDPR, DORA and NIS2 expect structured and tested incident response procedures.
Final Thoughts
Cyber resilience in 2026 is not about having documents. The difference between a contained incident and a business-wide crisis often comes down to how quickly your teams can execute the right actions at the right time.
That’s where experience matters.
At Cyber Management Alliance, we don’t just create playbooks—we design, validate and operationalise them based on real-world attacks.
As the creators of the NCSC Assured Building and Optimising Incident Response Playbooks course and global leaders in cyber incident response and tabletop exercises, we’ve helped hundreds of organisations transform static documents into battle-ready response frameworks.
Whether you’re:
we can help you close the gaps, reduce response time, and build true cyber resilience. Speak to our experts today to build or review your incident response playbooks and ensure your organisation is ready when it matters most.